The goal of this project is to write a firmware for all Conexant wireless chipsets from scratch. The advantages are :
- You will be able to run your wireless station on 100%-free software
- You can have high-quality wireless drivers, without suffering from firmware bugs or limitations that can’t be fixed because of proprietary licences
- You can hack whatever feature you want into the firmware
- You can use your wireless device as a powerful ARM development board, with a 946E core clocked at 30MHz
- With some electronics skills, you can add whatever you want to your wifi card (LCD, keypad, …). They have an I2C bus which can be easily tapped.
- You can learn how your device works in detail
Obviously, Conexant does not want us to do that with their chipsets, which are heavily covered by Non-Disclosure Agreements. So if this appeals to you, you are welcome to join the reverse engineering efforts 🙂
Supported devices
FreeMAC intends to support all Prism54 devices. For now :
- PCI devices are 100%-supported
- USB version 1 devices are 100%-supported
- USB version 2 devices are on their way to becoming supported
Status
- We can run arbitrary C code on the ARM. All the memory mappings are known.
- The PCI engine is completely done. We can take care of IRQs and DMA transfers nearly as good as the official firmware.
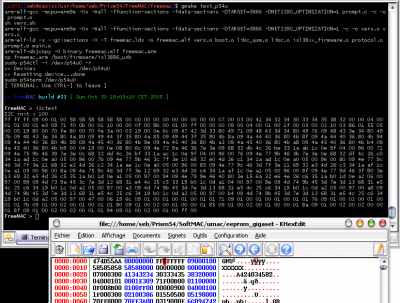
- Besides the normal PCI+DMA interface, we have interrupts + general-purpose communication registers-driven command-line interface for debugging the thing (also implemented as “UARTPCI” in the official firmware). This is what is shown in the screenshot.
- All this even works with a USB version 1 device.
- Most USB registers of the USB version 2 devices are known. We can do bulk transfers.
- The I2C bus is completely accessible. The configuration EEPROM of the device can be read without a hitch.
- The two LEDs of the device can be controlled. They are even functional PCI protocol frames which do this from the driver.
- The hardware cryptography accelerator registers have been identified, and we can already do some RC4. We’re still missing some algorithm and key setup, but this is not a priority anyway.
- The three internal timers of the chip are known.
- Few radio-related registers have been found.
If you want to know how we did this, see FreeMAC History.
How to try and develop FreeMAC
First, you need to install the ARM toolchain as described here.
Then, take a snapshot of the SVN repository (you can also use svn co svn://svn.tuxfamily.org/svnroot/prism54/freemac), and compile it with the “make” command. This will produce the “free mac. arm” file, that you can use like any other firmware.
Now, you need to set up the device driver.
p54u
p54u is able to take care of FreeMAC firmware since version 0.6.1. Install it the normal way, but before compiling it, edit driver/config.h and uncomment the line saying “#define WITH_FREEMAC”.
Then, just use the free mac. arm file as a drop-in replacement of the SoftMAC one. p54u will automagically detect you are using FreeMAC.
You can then have the FreeMAC prompt with this command :
# p54term /dev/p54u0
Islam
- Download and install the driver as outlined in http://jbnote.free.fr/prism54usb/
- Put the FreeMAC binary somewhere firmware_agent will find it (/usr/lib/hotplug/firmware/freeman for instance)
- insmod the driver (make load from the root directory should be okay)
- go to the src/utils/Islam-ctrl directory; do an islsmctrl -dev /dev/islsm0 -set name -name freeman or whatever you named the file to reflect the filename change
- go to src/utils/Islam-term; then execute islsm-term /dev/islsm0. Read the message, then have fun. Warning: on the 3887, triggering firmware upload will make the uart go awry.
Technical resources
Technical information about the chipset is available on the wiki, especially on this page and some (messy) reverse engineering notes are available here (general info) and here (radio specific).
You should also read the hardware register definitions in isl38xx_hardware.h.
If you want to “hunt” for hardware registers, I suggest you print out a copy of these documents. This makes assembler code reading and experimentations much easier.
